
Understanding Unified Threat Management: A Comprehensive Approach to Network Security in Modern Organizations

How Linux Training Helps Cybersecurity Professionals Secure Systems

Cyber Security Services in Frisco

Cybersecurity Excellence: Safeguarding Your Digital Future

Fortify Your Future: SG Computer’s Elite cybersecurity services in boston
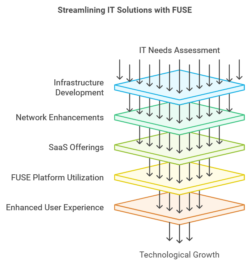
“Transforming Businesses with FUSE & Innovative IT Solutions”

Top 5 Cybersecurity Practices for New York-Based Organizations

The Ultimate Guide to Cybersecurity Services in New York

Why Cybersecurity Matters for New York Startups and Small Businesses

Cybersecurity Threats in New York: What You Need to Know Now

How New York Businesses Can Improve Their Cybersecurity in 2024

Cybersecurity in New York: Essential Tips for Businesses and Individuals

Top Cybersecurity Firms in New York: Protecting Your Business in 2024

Why Hiring a Chief Information Security Officer is Critical for Data Protection
Chief Information Security Officer vs. IT Director: Understanding the Differences

How a Chief Information Security Officer Can Strengthen Your Cybersecurity Strategy

The Role of a Chief Information Security Officer: Why Every Company Needs One

Testimonial from another Happy Client

Expert Cyber Security Services from OptivITy Limited

Boost your cyber defenses with our expert Cybersecurity Consulting Services!

Unlock the Secrets of Software Security!

Firewall Management Service
What Is Cybersecurity? Why Is Cybersecurity Important?

Renan Batista Adsply | Tips to Avoid Virus on the Internet

Renan Batista Adsply Shares Tips to Keep Personal Data Safe

Benefits of Cybersecurity Automation
CCNA Training In Kolkata by ICSS

Renan Batista Sequestro- Network Security

Visit Cybersecurity Pittsburgh

Enhance the Brand Visibility

Industrial IoT: The Manufacturing Sector’s Paradigm Shift – EvoortSolutions

Boost your Website Ranking and Performance

Best Strategy for Brand Building

Boost your Search Ranking

Increases Positive Returns

Professional Web Design Service

Information Technology Security

Exponentially Grow Your Business with SEO

Improve the Online Business by an Organic Way

Improve the Business to Acquire New Customers

Connect Potential Buyers Using the Internet

Connect the Customers through Online Business

Effective Way to Design to Reach More Leads

Online Solution to Increase the Sales

Custom Web Design to Interact the Customers

Cybersecurity Training California

Process of Managing Online Presence

Increase the Visibility in Organic Way