Understanding Unified Threat Management: A Comprehensive Approach to Network Security in Modern Organizations
The Evolution of UTM Solutions
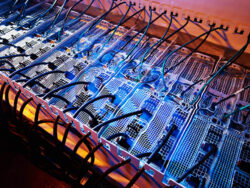
In today’s rapidly evolving digital landscape, organizations face an increasingly complex array of cybersecurity threats. The traditional approach of deploying multiple standalone security solutions has given way to a more integrated and efficient model known as Unified Threat Management (UTM). This security approach emerged in the early 2000s as a response to the growing need for comprehensive network protection that could be managed from a single platform. UTM solutions have since evolved from simple firewall-antivirus combinations to sophisticated systems that incorporate multiple security features and advanced threat detection capabilities.
Core Components of UTM Systems
At the heart of every Unified Threat Management solution lies a robust set of security features designed to protect networks from various threats. The firewall serves as the primary defense mechanism, monitoring and controlling incoming and outgoing network traffic based on predetermined security rules. Advanced firewall capabilities include stateful inspection, deep packet inspection, and application-layer filtering. Intrusion Detection and Prevention Systems (IDS/IPS) work alongside the firewall to identify and block potential security breaches in real-time. Anti-malware protection, including antivirus and anti-spyware components, safeguards against various forms of malicious software that could compromise network security.
Get More Insights On- Unified Threat Management